As you may have noticed, the Edgescan platform has recently rolled-out an new UI and here are the features you really need to know about. We are proud of the award-winning design and the improved functionality, feedback from users has been fantastic.
Validate Yourself
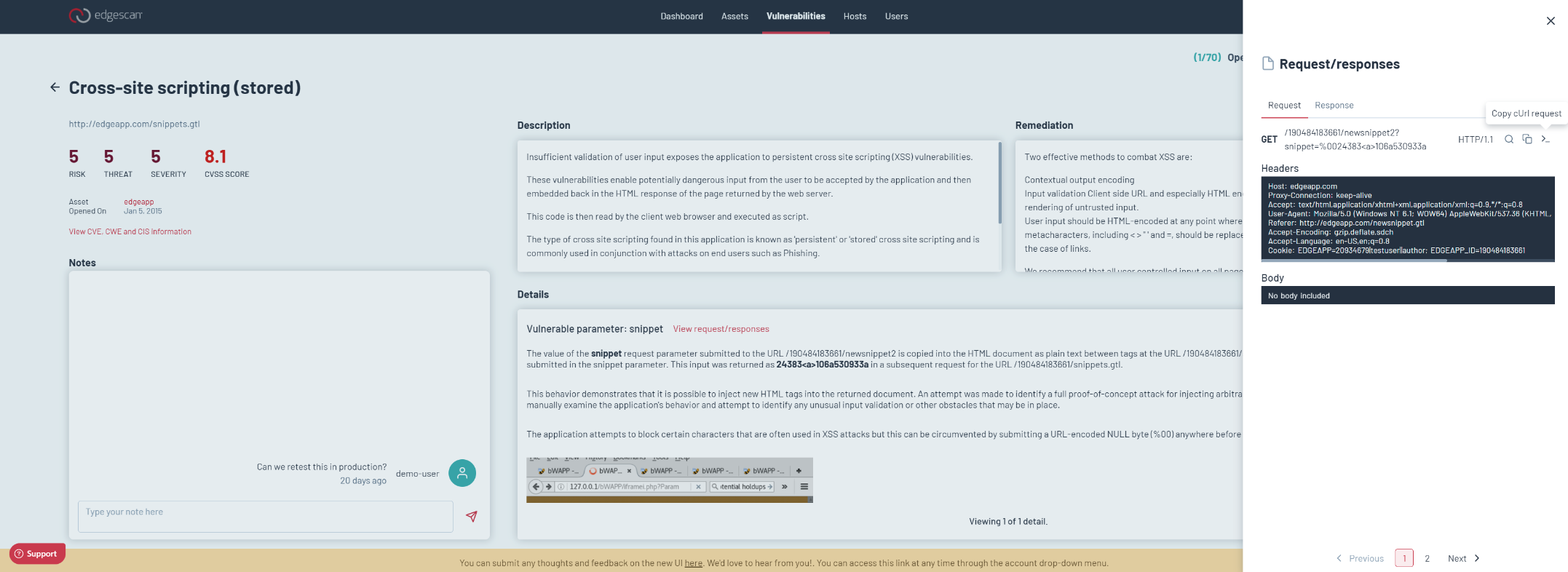
All application layer vulnerabilities can be recreated by copying a CURL or Raw request. This helps you understand the entire request and steps taken to reproduce the vulnerability.
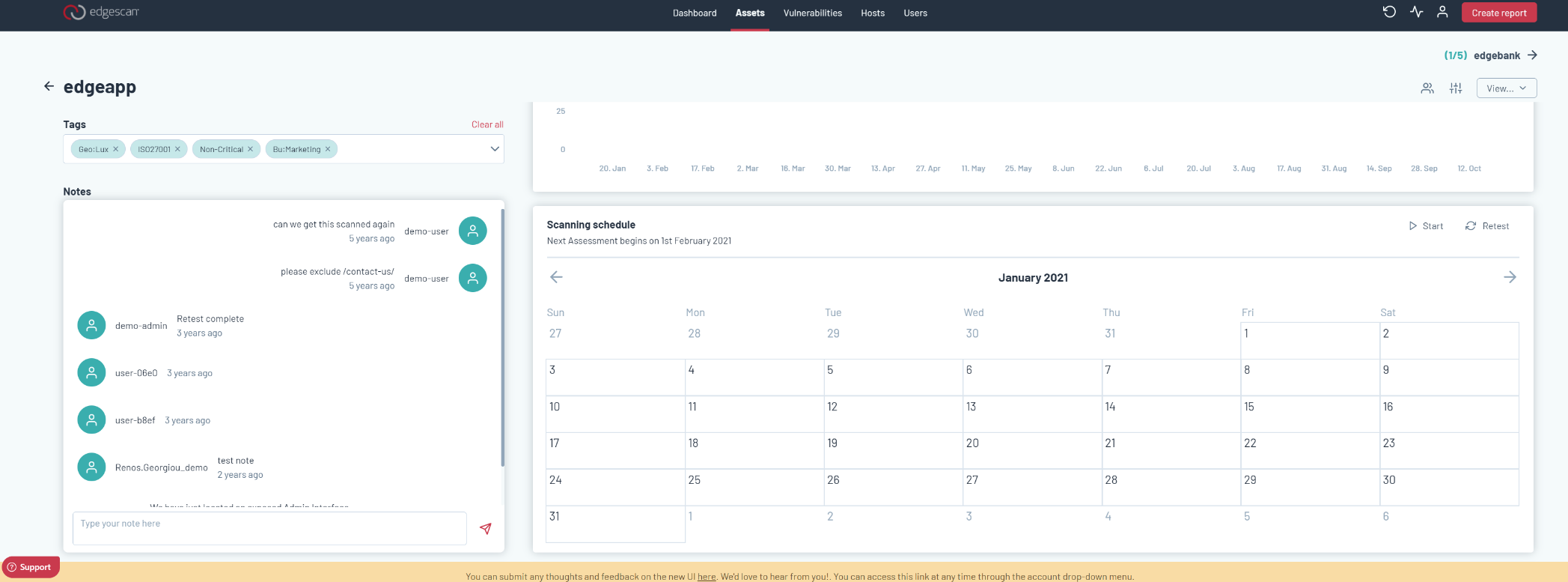
Retest
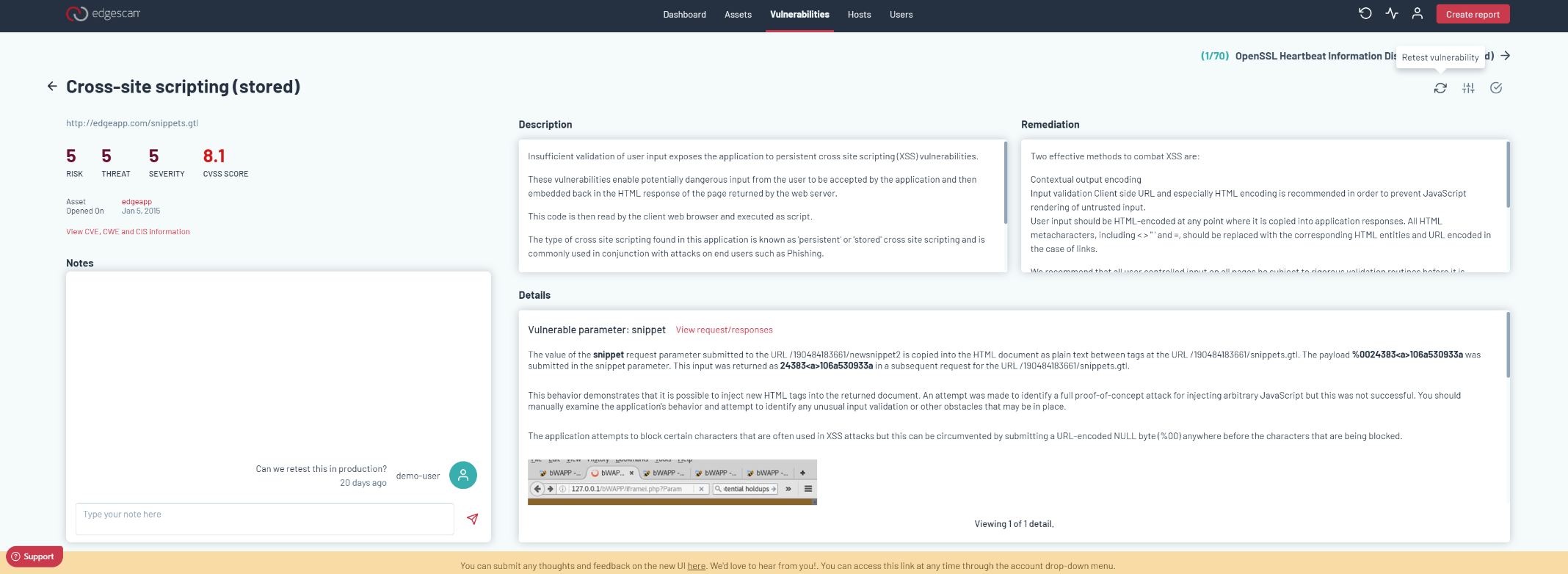
You can retest vulnerabilities on demand. So you’ve fixed a vulnerability, now hit “Retest” and bingo, Edgescan will validate to see if the issue is mitigated.
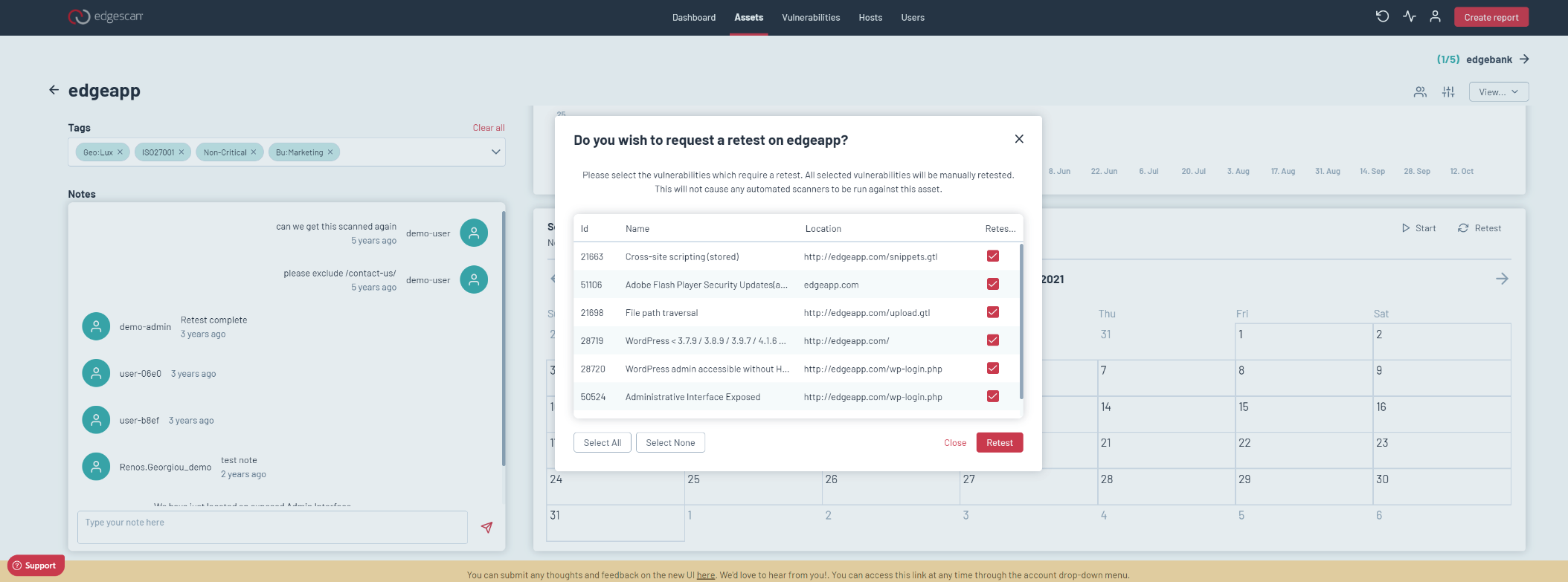
You can also retest all vulnerabilities or select whichever ones you want to retest via the Assets page.
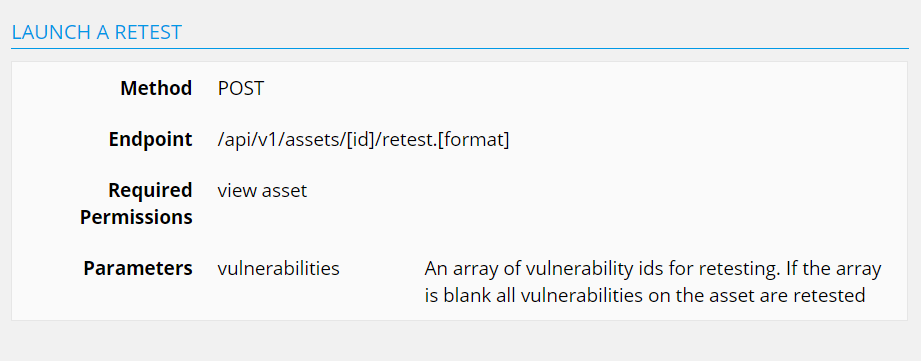
Retest via the API is via the retest endpoint
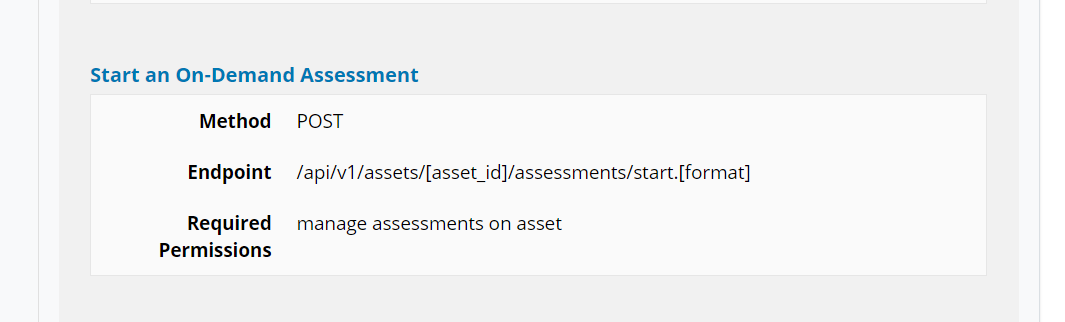
On-Demand assessment
If you need an on-demand assessment, say you just deployed a new feature or need to get an assessment randomly you can do this via the Assets page “Start” or the API.
Start an on-demand assessment via the API.
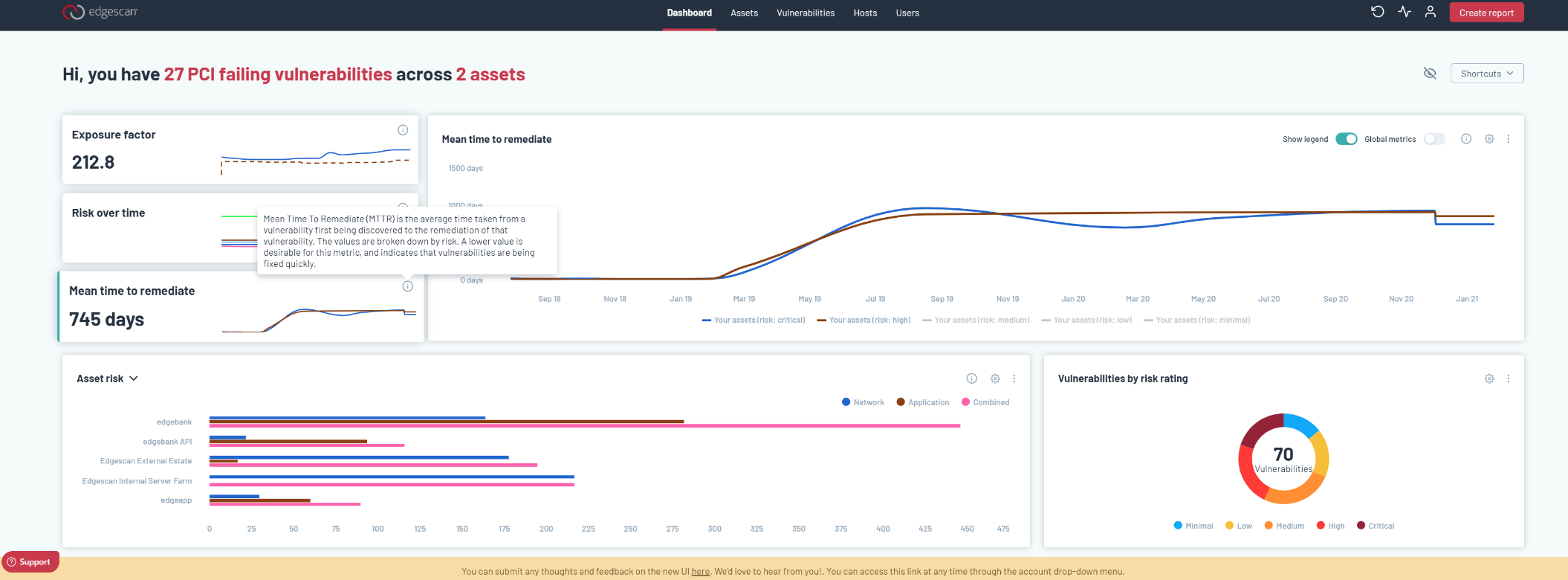
Metrics
The new Edgescan UI provides a huge array of metrics
From MTTR, Exposure factor, Risk over time and Asset Risk
API Integration
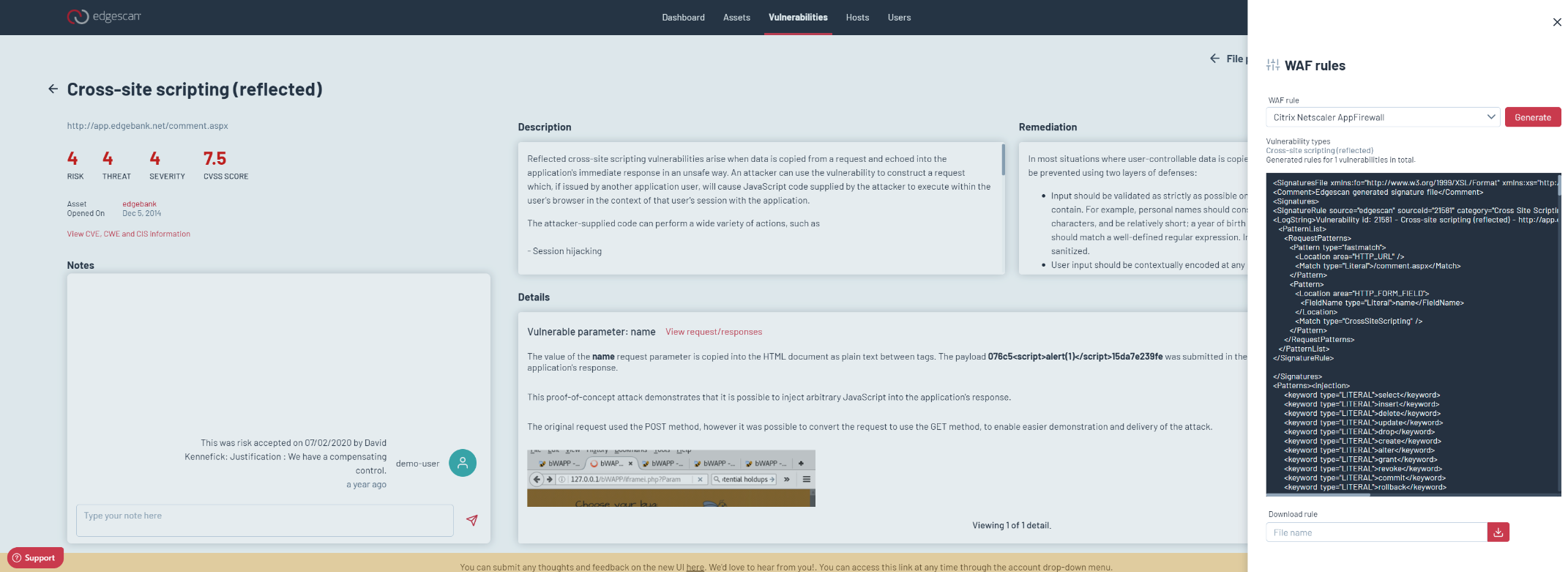
Generate WAF Rule:
You can auto generate a Web Application Firewall rule for specific WAF’s. This may help you virtually patch the vulnerability if you can’t make the code fix.
This can be done also via the API.
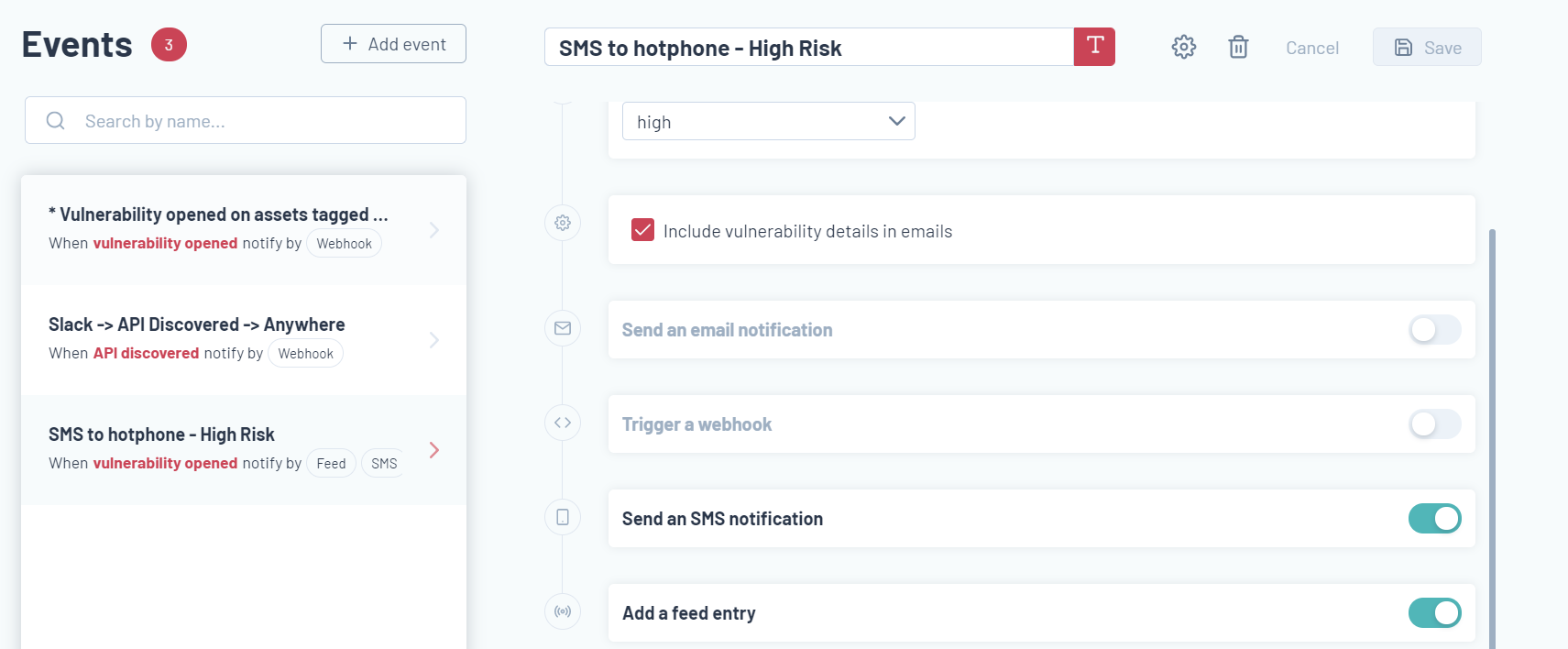
Setting up events:
Events keep you informed – Keep informed based on what matters to you. Be it a newly discovered vulnerability, a closed vulnerability, a newly discovered host, an API discovery, ports open on a host etc.
Events can integrate to the likes of Jira, Teams, Slack, Email, SMS etc
Like what you see? Contact Edgescan Sales to arrange a POC or Request a Demo.
Subscribe to the Edgescan blog to receive updates.